Blog
Refresh Content
Traffic Analysis: Unveiling Cybersecurity Threats Through Network Patterns
Uncover hidden cyber threats by analyzing network traffic patterns, even when data is encrypted. Learn the art of traffic analysis.
Read MoreMar 29, 2025
Created: 3/29/2025, 4:17:13 PM
Updated: 3/29/2025, 4:17:13 PM
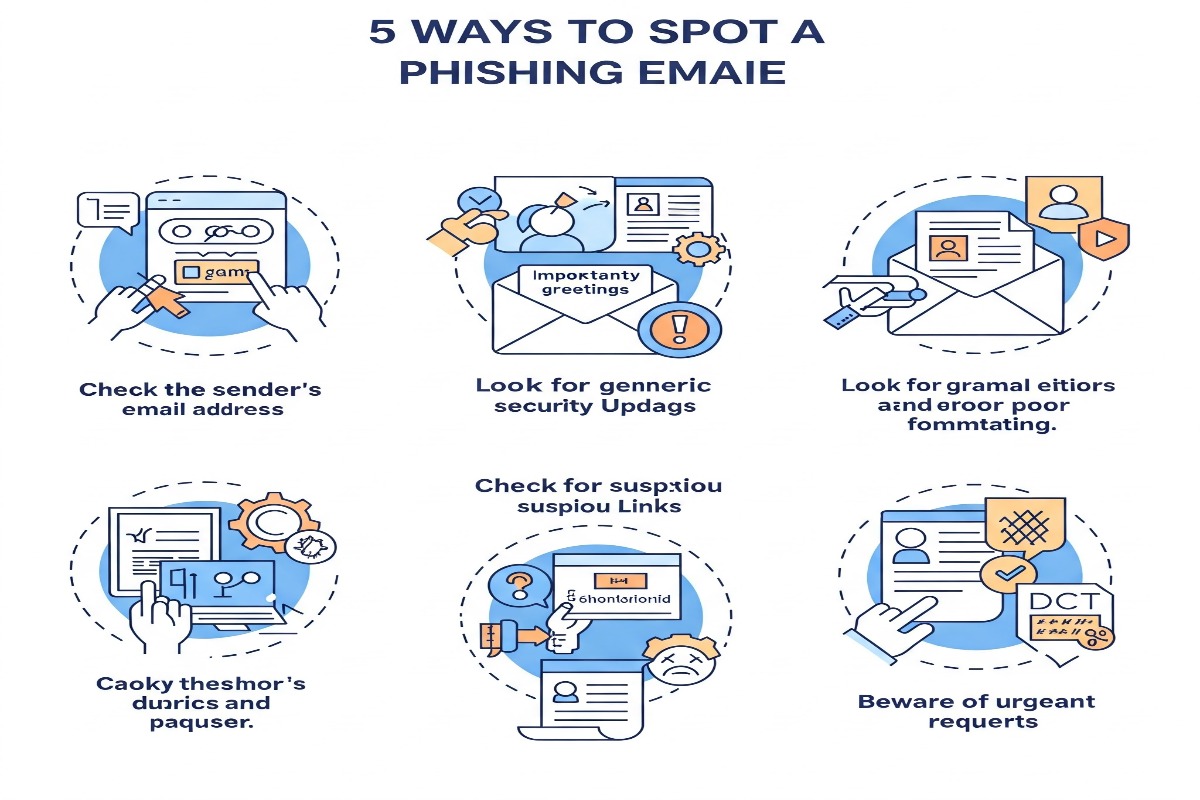
5 Ways to Spot a Phishing Email
Stay vigilant online by verifying sources, questioning urgency, and protecting your personal information.
Read MoreMar 22, 2025
Created: 3/22/2025, 3:36:21 PM
Updated: 3/22/2025, 3:36:21 PM

Fortifying Your Digital Fortress: The Unsung Hero - The Firewall
Examining evolving cybersecurity threats and actionable defense strategies for organizations in today's expanding digital landscape.
Read MoreMar 22, 2025
Created: 3/22/2025, 4:47:55 PM
Updated: 3/22/2025, 4:47:55 PM

The Future of AI in Cybersecurity
Explore how AI is being used to detect and prevent cyber threats.
Read MoreMar 22, 2025
Created: 3/22/2025, 5:35:25 AM
Updated: 3/22/2025, 9:47:00 PM